There appears to have been a large number of mobile phones in the news recently, thanks primarily to the rising trend for cheap handsets and the highly anticipated launch of the iPhone 6. The technology that underpins mobile media has also hit the headlines in the last month, however, this was all for more sinister reasons. More specifically, August 31st saw a number of supposedly nude celebrity photographs published to sites including 4chan, Imgur and Reddit. Referred to as ‘The Frappening’, this series of images quickly became one of the fastest growing threads in Reddit history before being deleted. The pictures were in fact fabricated, and had been created using readily available hacking technology that reportedly has the capacity to infiltrate iCloud’s popular Photo Stream feature.
The Importance of Safeguarding yourself in the iCloud
This serious security breach underlines the vulnerability of iCloud and this type of technology. While it is extremely useful and enables individuals to store images, contact details and MP3 files in a single online space, it’s also susceptible to sophisticated cyber hackers. For anyone with an iPhone and access to iCloud, there is a pressing need to operate securely and in a way that does not compromise their most sensitive data. Consider the following steps towards achieving this: –
1. Understand the Importance of Physical Security
As a general rule, it can be easy to become preoccupied with creating strong passwords for devices and individual iCloud accounts. While this is important, however, it is also crucial that you safeguard the physical security of your hardware and ensure that each individual device is tracked at all times. If your iPhone or tablet is set to remember your iCloud password, for example, anyone who comes into contact with the device can easily access any data or image that have stored in iCloud. So even if you have a strong, uniform password for every account, you will need to deny others access to your devices where possible and keep track of their location at all times.
2. Change your Approach to Creating Passwords
Historically, online service providers have advised users to create strong and unique passwords with a combination of letters, numbers and special characters. This is not enough to safeguard your iCloud against the threat of cyber thieves however, simply because hacking software is designed to successfully bypass single words and alpha-numeric terms. Instead, you should consider using phrases to protect the integrity of your account, which are easy for you to remember as an individual but extremely difficult for existing software to translate. This will add an additional layer of security to your iCloud data, while also making it easier for you to remember your password and access images, files and sensitive information.
3. Use Only Secure Wireless Networks to Transfer Data
As a basic security measure, Apple encrypts all files that are sent to iCloud and stores them in this format. This type of rudimentary measure can be successfully negated by sophisticated hackers, so it’s important that you take additional steps when transferring data to iCloud. It is imperative that you use only secure wireless networks to connect with iCloud, for example, such as those that you control through an alpha-numerical password. Public networks such as wireless hotspots or those accessible through coffee shops should be avoided at all times, as these are far more vulnerable to security breaches.
4. Protect the Files on your Device as well as those in iCloud
While Apple may encrypt files sent from synchronised devices once they have been stored in iCloud, they do not extend this courtesy to those on the handset itself. So if your device is connected to iCloud but not protected with a passcode, or by the option of requiring the user to approve access each time that the USB is plugged in to a new machine, it is possible for hackers to utilize a number of third-party programs and copy files directly from the handset. With this in mind, be sure to create a simple four-digit passcode that enables you to lock your phone, as this will encrypt all files and make them inaccessible even if they are transferred over. This is a viable option with iOS 7 on the iPhone 4S, iPad 2 and all subsequently released devices.
5. Encrypt all Sensitive Documents and Images to your Hard Drive
On a similar note, it is worth encrypting all synced and sensitive data that exists on your hard drive. While the encrypted files in iCloud may be relatively secure, this means little if they are openly accessible through your hard drive, smartphone handset or tablet device. In addition to this, Apple may be required to turn over even sensitive and personal user data if they are compelled to through a court subpoena. Although this represents a minimal risk, it is crucial that you save files such as health care records or financial information in an encrypted format in their original location. This is an additional security measure that safeguards the integrity of the data stored in iCloud.
6. Be Wary of Siri
As a conscientious iPhone and iCloud user, you will need to be aware of all potential security gaps when active online. Even when your device is locked with a four-digit passcode, for example, it’s default setting is to allow users access to the intelligent personal assistant referred to as Siri. A key part of the apple support network, it helps users to complete actions by audio instruction without the need to type or enter keywords. This creates the potential for a huge security gap, as anyone can ask Siri questions that will return data, contacts and additional stored information. This is something to be wary of, especially when establishing your phone’s settings after purchase and storing sensitive data.
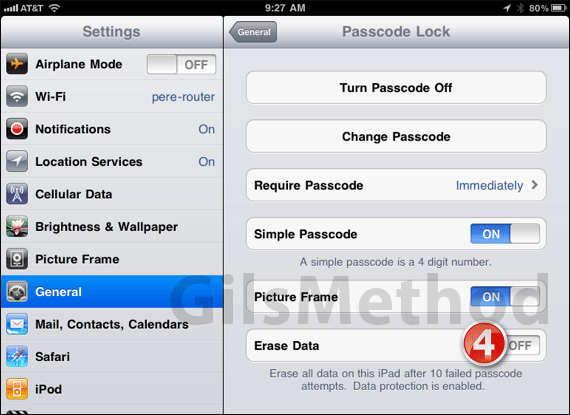
7. Set your Phone to Wipe Data if too Many Unsuccessful Access Attempts are Made
If you access your iPhone settings, there is an option located at the bottom of the ‘Passcode Lock’ page beneath Siri which is titled ‘Erase Data’. Simply enabling this feature, you can automatically set your iPhone to
8. Integrate Two-factor Authentication with your Account
We have already discussed the vulnerability of passwords, especially those that are generic in their nature or reused across multiple online accounts; this vulnerability can be offset by the integration of two-factor Authentication with your accounts. Apple offers this as an optional feature for iTunes and iCloud users, and it works simply by forcing individuals to enter both a password and a unique device code before they access the account. These codes are usually sent via SMS upon registration, and they prevent unknown or unverified devices from accessing your data. This is a simple step, but one that can provide considerable peace of mind to Apple customers.
9. Regularly change your Security Questions and Answers
Online users are often urged to regularly refresh their account passwords, in order to partially negate the threat posed by hackers. While this is good advice, there are other aspects of user-controlled iCloud security that require a similar proactive approach. For example, Apple will always prompt users to use security questions and answers to help control their accounts, and it is important that you change these regularly while also using a combination of truthful and inaccurate data. After all, a hacker may only need to access your emails or synced accounts to identify the name of your partner or a beloved pet, so safeguard your iCloud data by refreshing the questions every month or so and using incorrect answers where possible.
10. Link your iCloud to a Current and Accessible E-mail Account
Your iCloud relies heavily on the primary email address that you use. Whether you need to register, log in or reset your password you will need a viable address to secure your account. It is therefore crucial that the iCloud is always associated with a current and accessible email account, rather than one that is now inactive. This is a detail that many users overlook, but idle email accounts represent an easy target for cyber thieves. So be proactive and update your primary email address where necessary, whether you have created a completely new account or have received a reissue address as a result of changing Internet service providers or employers.
Featured photo credit: Falko MD / Flickr via flickr.com